
The protection of data is a crucial concern for individuals, businesses, and organizations of all sizes. With the increasing reliance on technology for storing and transmitting sensitive information, the threat of data breaches and theft has become a major issue. In 2022, there were more than 2000 publicly disclosed data breaches, with 60% being a result of hacking. Affected companies and individuals were at risk of financial and reputational losses, compromised data, and sometimes legal liability.
To mitigate these risks, several methods have been developed to protect data from unauthorized access and manipulation. In this article, we will detail the top 5 methods of protecting data.
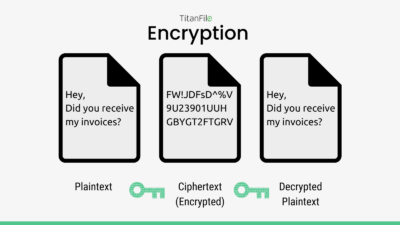
1. Encryption
Encryption is a fundamental component for protecting personal data. It involves converting sensitive information into a coded form, making it unreadable to anyone without the proper decryption key. Only the authorized user, who possesses the decryption key, is able to decode and view the information. This method is widely used to protect sensitive data during transmission over the internet, as well as to secure data stored on devices, such as laptops and mobile phones. Additionally, encryption algorithms, such as AES and RSA, are used to scramble the data, making it virtually impossible for unauthorized users to access it.
One of the key benefits of encryption is that it offers a high level of security, even in the event of a data breach. If encrypted data is stolen or otherwise accessed by an unauthorized party, it will be unreadable and therefore, useless to the attacker. Additionally, encryption also helps organizations comply with privacy regulations and standards, such as the General Data Protection Regulation (GDPR) and the Payment Card Industry Data Security Standard (PCI DSS).
However, encryption is not foolproof and must be implemented properly to be effective. For example, if the encryption key is lost or stolen, the encrypted data will be inaccessible, even to the legitimate owner. Additionally, encryption algorithms can be broken, particularly if they are not updated to keep up with advances in technology and attacks by malicious actors.
2. Backup and Recovery
Backing up data regularly is an important aspect of data protection, as it ensures that data is preserved in the event of data loss or corruption. By creating copies of data and storing them in a secure location, organizations can quickly recover their data in the event of a disaster. Many companies use cloud-based storage services, such as TitanFile, as they provide a secure and reliable way to store and recover data. As well, experts recommend using the 3-2-1 method for backing up data. The 3-2-1 data backup method involves backing up three copies of data on two local devices (i.e. original device, external hard drive) and one off-site (i.e. cloud-based).

One of the key benefits of backup and recovery is that it allows organizations to quickly recover from data loss, minimizing downtime and reducing the risk of permanent data loss. Additionally, backup and recovery solutions can also provide an additional layer of security, as they can be used to restore data to an earlier point in time, effectively undoing any unauthorized changes or deletions.
Although beneficial, data backup and recovery are only as successful as the environment they’re placed in. Backups must be stored in a secure location, such as an off-site facility, to protect against theft, natural disasters, and other risks. Additionally, backups must be tested regularly to ensure that they can be successfully restored in the event of a disaster.
3. Access Control
Access control is a method of restricting access to sensitive information to only authorized users. This can be achieved through the use of passwords, multi-factor authentication, and role-based access control. These methods ensure that only those with the proper authorization can access sensitive data, reducing the risk of data breaches and unauthorized access.

One of the key benefits of access control is that it helps establish accountability within organizations by enabling them to track and monitor who has access to what resources, and who performed which actions, reducing the risk of insider threats. Additionally, access control improves efficiency by streamlining the management of access permissions; reducing the time and resources required to manage access for large numbers of users.
Similar to all data protection methods, access control must be implemented properly in order to be effective. For example, passwords must be strong and unique, and multi-factor authentication must be used to provide an additional layer of security. Additionally, access control systems must be regularly updated and tested to ensure that they are functioning properly and protecting sensitive data from unauthorized access.
4. Network Security
Network security refers to the measures used to protect information and assets stored on computer networks from unauthorized access, theft, or damage. This can include using firewalls to block unauthorized access, implementing intrusion detection systems to monitor for and prevent cyber-attacks, and using encryption to protect sensitive information transmitted over the network. Regular software updates and employee training can also play an important role in reducing the risk of cyber-attacks.

One of the key benefits of network security is its role in confidentiality. Network security helps to ensure that sensitive information is kept confidential, preventing unauthorized access and data breaches. It also enables organizations to meet regulatory requirements and industry compliance standards, such as HIPAA and PCI DSS. Most importantly, network security plays a huge role in risk management. It helps organizations identify and mitigate potential security risks, reducing the likelihood of security breaches and other incidents.
It’s important to note that a successful network security infrastructure requires an educated IT team. Network security systems can be complex and difficult to manage, requiring specialized knowledge and expertise to configure and maintain them effectively. Additionally, as threats evolve network security measures must be constantly updated and improved to keep pace with evolving threats and new attack methods.
5. Physical Security
Lastly, physical security is another important component of data protection, as it involves the measures used to secure physical devices and facilities that store sensitive information. This can include locking devices in secure storage cabinets or vaults, implementing access control systems with biometric authentication or key cards, and installing security cameras and alarms in sensitive areas. Portable devices, such as laptops and mobile phones, are also vulnerable to theft or loss and can be protected with encryption, secure passwords, and remote wipe capabilities.

A clear positive of physical security is the confidence it provides organizations. Physical security measures can give organizations confidence in the integrity and availability of their backup data, reducing the risk of data loss or corruption. Organizations can also reduce costs by protecting backup media since they avoid the cost and time associated with data recovery efforts, such as data restoration from tapes or hard drives.
However, the main drawback of physical security is the human aspect. 95% of cybersecurity data breaches are a result of human error – despite physical security measures, human error can still occur, such as misplacing backup media or leaving it unsecured. It’s important to keep track of backed-up media locations and ensure they are secure before storing them away.
Conclusion
In conclusion, data protection is a critical concern for individuals and organizations in today’s digital age and needs to be addressed at all stages of a file’s journey. A comprehensive approach to data protection that includes encryption, backup and disaster recovery planning, access control, network security, and physical security can help ensure the security and confidentiality of sensitive information. It is important to regularly assess and update security measures in order to keep up with advances in technology and the evolving threat landscape.
Share this article with your network if you think they should protect their data!