For the past year and a half, the world has been facing a dangerous obstacle. Here enters the age of the virus—from both a health and a digital platform. The world continues to be challenged by COVID-19, a virus that continues to disrupt the many different sectors of each country and most importantly, the people’s way of living. Thanks to the huge strides in medication, vaccines have saved many lives. If anything, these unexpecting times have served as a wake-up call to many—especially those who come unprepared.
However troubling these scenes may be, the world continues to grow, to evolve. The work-from-home option given to employees has served many families abundantly. With the rising numbers of people following this trend, cybersecurity must work harder. According to Cybersecurity Ventures, it is estimated that 2021 will see a loss of $6 trillion solely from cybercrime. With these numbers, it’s inevitable to prepare yourself a cybersecurity checklist.
Today’s digital landscape is complicated, but only because cybersecurity threats have strived to evolve alongside it—transforming from traditional brute force to well-thought-of attempts. One thing remains consistent, and that is a hacker’s relentless attempts to breach businesses and take a hold of confidential information. Numbers are on the rise, and now is the time to apply security’s best practices.
While it is difficult for a business or an organization to foresee and completely eliminate the threats of cybersecurity, there’s a reason why cybersecurity checklists and IT security checklists exist—and that is to strengthen all forms of cybersecurity. The next years will be challenging but make it less with this list of top items to include in your cybersecurity checklist.
1. Use a Secure File-Sharing Solution
 It goes without saying that mitigating cybercrime starts within the business or organization. One of the best items to tick off from your cybersecurity checklist is definitely using a secure file-sharing platform. Secure file sharing is the act of sending forms of documents digitally in a manner in which unauthorized users are prohibited from seeing this shared information. If your business holds a plethora or a handful of confidential data, then sharing files securely should definitely rank higher up on your list—especially when these data are shared only with a few select people or groups who have all the rights to sensitive information and numbers.
It goes without saying that mitigating cybercrime starts within the business or organization. One of the best items to tick off from your cybersecurity checklist is definitely using a secure file-sharing platform. Secure file sharing is the act of sending forms of documents digitally in a manner in which unauthorized users are prohibited from seeing this shared information. If your business holds a plethora or a handful of confidential data, then sharing files securely should definitely rank higher up on your list—especially when these data are shared only with a few select people or groups who have all the rights to sensitive information and numbers.
Typically, secure file sharing is paired with a combination of numerous security protocols such as data encryption, multi-factor authentication, and other security controls before being granted access to the files. Thankfully, there are many types of secure file sharing systems for you to choose from. Each of which comes with its own varying features, security protocols, and even prices to cater to your every need.
Want a solution that’s as easy to use as email? Give TitanFile a try!
2. Enforce a Strong Password Policy

Will you look at that? Passwords stay important, relevant, and no matter how simple—very effective. Similar to best practices for email security, your cybersecurity checklist must realize the importance of strong passwords too. To be frank, “123456” isn’t the best password choice out there. Collectively, over 3 million people use these numbers as their frontline for security and it is highly concerning.
The power of passwords doesn’t only concern your personal Facebook accounts and business emails, but you should also realize that it serves as the frontline of defense to cover your overall cybersecurity. IT policies should instruct employees to use complex passwords. A combination of upper and lower case letters, numbers, and special characters can only put you one step ahead of cybercrime. Veering away from birthdays, ID numbers, hometowns, or any personal information is highly encouraged, too.
Motivate and not only require personnel to change their passwords at least four times or more per year. Past passwords are discouraged to be of use again. Whether it’s your closest friend or family member, no one is allowed to know your password until deemed personally necessary.
3. Use Anti-Malware and Anti-Virus
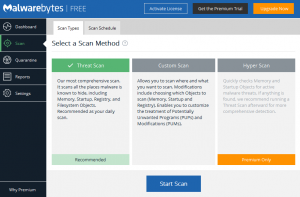 Solely developed to fight against cyber threats are the anti-malware and anti-virus systems. It’s an obvious weapon against cybercrime and one of the best practices for security. Just so much as vaccines work against COVID-19, anti-virus systems work just the same. Though it may seem a little bit repetitive, these anti-malware programs do work.
Solely developed to fight against cyber threats are the anti-malware and anti-virus systems. It’s an obvious weapon against cybercrime and one of the best practices for security. Just so much as vaccines work against COVID-19, anti-virus systems work just the same. Though it may seem a little bit repetitive, these anti-malware programs do work.
Businesses and organizations need to ensure that their programs are up-to-date and are always set to check for updates, scan computers on a set schedule, and religiously lookout for media inserted from flash drives and external hard drives. If larger agencies and corporations are involved, each workstation must be configured to report the antivirus status to a centralized station to inform about unforeseen malware and update accordingly.
Having antivirus software on a device does not always guarantee the safest endings nor the absolute protection one needs from evolving cybercrime methods. However, updating and even just getting one saves the employees trouble while acquiring new defenses against ransomware, spyware, and other forms of viruses.
4. Conduct Routine Security Awareness Training for Staff
 COVID-19 has not only brought the world into shambles but has also contributed to a new wave of phishing. These attacks are designed to take advantage of the distressed employees caused by the pandemic. Security awareness training belongs to the cybersecurity checklist for good reason. This is to educate employees on the current attacking methods like phishing, pharming, and ransomware attacks used by hackers to gain access to computers. It’s not all about attacks, though, as this is also a great opportunity for the organization to review firm policies and the cybersecurity checklist.
COVID-19 has not only brought the world into shambles but has also contributed to a new wave of phishing. These attacks are designed to take advantage of the distressed employees caused by the pandemic. Security awareness training belongs to the cybersecurity checklist for good reason. This is to educate employees on the current attacking methods like phishing, pharming, and ransomware attacks used by hackers to gain access to computers. It’s not all about attacks, though, as this is also a great opportunity for the organization to review firm policies and the cybersecurity checklist.
For example, although spam filtering has been used effectively to identify malicious emails, other forms of spam emails may come off as authentic—making their way into an inbox. At that point, you’re only a few steps away from exposing an organization-worth of information—and very sensitive ones at that. To counteract this, employees must undergo cybersecurity training highlighting the mitigation and identification of potential attacks.
On the topic of employees, organizations must also do background checks on potential staff members before granting them access to resources and information. Unfortunately, today’s internet connectivity could pose more threats when paired with tiny, yet very powerful USB storage devices as they are enough to copy or even erase information without leaving any tracks.
5. Have a Data Breach Response Plan
Even if you religiously tick off the four mentioned items in your cybersecurity checklist, adopting these solutions does not guarantee an entirely safe organization—as previously stated also. Unfortunately, all businesses must prepare for the worse—and the worse comes in the form of a cyber-attack. In anticipation of the occurrence, an organization must maintain effective emergency recovery policies. In simpler form, have a data breach response plan.
This plan must be able to facilitate and organize the company’s effort in containing an attack. In this effort, employees must be assigned to consistently maintain and update the plan to ensure the speedy recovery of important data, networks, systems, and numbers. If an attack does happen, communication channels between these employees must be observed all throughout the process. For cybersecurity or an IT checklist, a data breach response plan should be their pillar.
Aside from when a data breach occurs, the plan involves many different steps. It could also take on the form of documenting the events leading up to the discovery of the breach and developing a communications plan to reassure the employees of their safety.
